Password Masking
A few months ago, Jakob Nielsen wrote an essay pointing out that masking passwords causes usability problems. Since users can't read the passwords they are entering, they are likely not to notice any mistakes they might make. He writes:
It's time to show most passwords in clear text as users type them. Providing feedback and visualizing the system's status have always been among the most basic usability principles. Showing undifferentiated bullets while users enter complex codes definitely fails to comply.
He also claims that since most of the time nobody is looking over your shoulders while you're entering a password, leaving passwords unmasked should not be a security issue.
Interestingly, security technologist Bruce Schneier at first agreed with Nielsen, writing:
Shoulder surfing isn't very common, and cleartext passwords greatly reduces errors. It has long annoyed me when I can't see what I type: in Windows logins, in PGP, and so on.
He later changed his mind, writing that he might have been wrong:
Password masking definitely improves security; many readers pointed out that they regularly use their computer in crowded environments, and rely on password masking to protect their passwords. On the other hand, password masking reduces accuracy and makes it less likely that users will choose secure and hard-to-remember passwords, I will concede that the password masking trade-off is more beneficial than I thought in my snap reaction, but also that the answer is not nearly as obvious as we have historically assumed.
While I usually use my computer where nobody can see me enter a password, I do sometimes use it in a coffee shop or in a meeting room where other people could see me enter a password. But a more likely situation is that I'm helping somebody else with a problem on their computer. I do prefer to not know the passwords my friends use, so I really appreciate password masking.
Obviously, there are cases where password masking is useful, and there are cases where it is annoying. What's the best solution here?
Some password fields default to masking, but let the user turn it off. I have never bothered to turn password masking off when one of these password fields came up; the work required to turn masking off (typically, clicking on a checkbox) is bigger than the expected work caused by a wrongly typed password. Usually, I get the password right. And even if I get it wrong, most of the time this merely causes an error message to appear, which can be discarded quickly with a single key press. Turning masking off is more work than it is worth. Letting the user turn masking off seems to be a poor solution.1
On Twitter, Oliver Reichenstein has just pointed out another idea which solves at least part of the problem without compromising security. Chroma-Hash is a jQuery Plugin which uses a one-way2 hash function to turn a string into a set of colors:
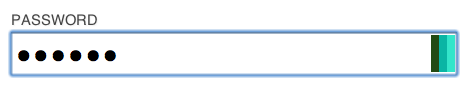
On the Chroma-Hash site, this is used in a registration form to show whether the user has entered the same password twice. However, the same color hashing idea can be used on any normal login form. After entering the password a few times, the user would get used to the color patterns appearing while he types the password. Should he make a mistake, or should Caps Lock be on by mistake, the user would immediately notice this error due to the unusual colors.
At the same time, the colors would be useless to an antagonistic observer, since these colors could not be used to find out the actual text entered into the password field.
Lotus Notes uses a similar system. Instead of using colors, it shows hieroglyphs. Something like Identicons could also be used.
You can read more about Chroma-Hash on this blog post.
-
On Twitter, peoun asks what I think of the iPhone's password field. If you haven't seen it, the iPhone's password field hides all but the last character; the last (or most recently typed) character is shown in plain text. Frankly, I'm not really sure whether I like this. In fact, when I use my iPhone to type a password, I look at the keyboard (which already shows the typed character). I barely even notice the password field. I'm not sure if the iPhone's password field is more usable than a regular password field, and I'm not sure how much security you lose by showing the last character in plain text. If implemented on a desktop system, it would definitely offer additional security compared to a plain old text field, but it would probably not thwart shoulder surfing password theft. ↩︎
-
"One-way" as in "hard to reverse." See the blog post for more information on this. ↩︎
If you require a short url to link to this article, please use http://ignco.de/135